- Lifetime Solutions
VPS SSD:
Lifetime Hosting:
- VPS Locations
- Managed Services
- Support
- WP Plugins
- Concept

If you manage a WordPress website, there is one type of cyber threat that security researchers consistently flag as the most widespread problem in the ecosystem, Cross-Site Scripting, universally known as XSS. It is not a glamorous-sounding attack, and that is partly why so many site owners underestimate it. But make no mistake: XSS is responsible for a significant portion of WordPress compromises every year, from small business blogs to large e-commerce stores processing thousands of transactions daily.
Secure WordPress hosting
Preventing XSS attacks takes secure code, updates, permissions, and a hosting stack you can manage. Voxfor VPS gives WordPress owners dedicated resources for safer sites and stronger server-level control.
The XSS vulnerability was the most common type of vulnerability by far, and almost half of all recently reported WordPress vulnerabilities comprised XSS, as per the Patchstack State of WordPress Security report. XSS alone contributed 34.7% of all reported vulnerabilities in WordPress in the first half of 2025, almost twice as many as the next most frequent category. Wordfence, a widely used security system in WordPress, thwarted more than 31 million attempts of XSS exploits within 30 days. That is not theoretical numbers. They are actual attacks on actual websites, and the rate is increasing.
This guide will walk you through what XSS actually is, how attackers exploit it on WordPress, what the real-world consequences look like, and, most importantly, exactly what you can do to protect your site, whether you are a developer writing custom code or a site owner with no programming background.

Cross-Site Scripting is a type of injection vulnerability where an attacker manages to place malicious JavaScript (or other client-side code) into a web page that other users then view. The browser has no way of knowing the injected script is not a legitimate part of the page, so it executes it without hesitation.
The name Cross-site Scripting is due to the history of web security, where attackers would inject (into) one site, which would execute in the context of another. The name has become a name, though more modern XSS exploits are typically smaller and may entirely occur within a single site.
On WordPress specifically, XSS is so common because WordPress is a dynamic, database-driven platform, content is generated on page load, stored in a database, and rendered through themes and plugins. Any point in that chain where user-supplied data flows into output without being properly sanitized and escaped is a potential XSS entry point.
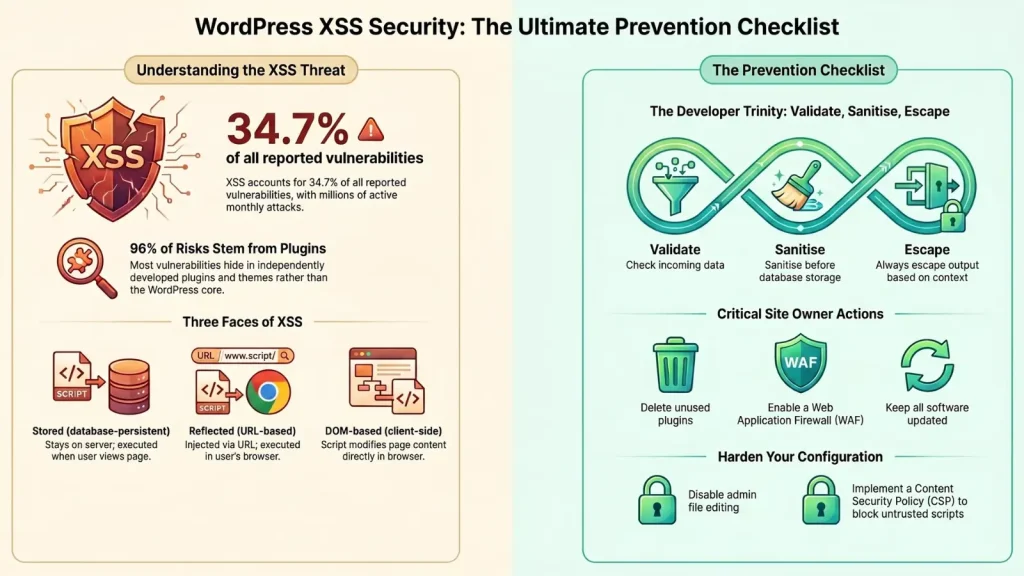
Understanding how XSS works in practice requires understanding the three main categories of the attack. Each has a different mechanism, different persistence level, and different severity.
Persistent XSS (also known as Stored XSS) is thought to be the most dangerous. In a stored XSS attack, the malicious script is stored directly to the database of the site, usually via a comment form, custom field, contact form, review submission or any other user-submission resource that stores data on the server.
Once stored, the script runs automatically every time any user loads the page where that content appears. A single successful stored XSS injection can therefore affect every visitor to a given page, including administrators, without requiring any further action from the attacker.
A real-world example: In 2024, security researchers at Fastly documented active exploitation of stored XSS vulnerabilities in several popular WordPress plugins, including WP Statistics (600,000+ active installs) and WP Meta SEO. In the WP Meta SEO case, attackers injected a payload via crafted 404 requests that was then stored in the database. When an administrator opened the redirect management page, the payload executed in their authenticated browser session, potentially handing full site control to the attacker.
Blind XSS is a sub-category of stored XSS worth understanding separately. The injected payload is not rendered on a public-facing page, instead, it fires when a back-end user, such as an administrator, opens an admin panel section, like a feedback inbox or site statistics page. Because the attack is invisible to external observers, it can persist undetected for a long time.
Reflected XSS is more interactive and short-lived. The malicious script is embedded in a specially crafted URL, typically inside a search query, an error message parameter, or another URL argument. When a victim clicks that link, the server reflects the payload in the page response, and the browser executes it.
Reflected XSS generally requires some form of social engineering: the attacker must convince a target (ideally an administrator with elevated privileges) to click the crafted link. This might come through a phishing email, a fake customer support message, or a link shared on social media. Because the payload is never stored, it evaporates after that single interaction, but the damage it causes in one click can be significant.
DOM-based XSS is unique in that the attack takes place entirely within the victim browser, with no involvement from the server. The vulnerability lies in client-side JavaScript that reads data from an untrusted source, most often a URL fragment or query parameter, and writes it to the page using unsafe methods like innerHTML.
Because no HTTP request carrying the payload reaches the server, DOM-based XSS cannot be detected through server-side logging, making it especially tricky to identify and block. A classic example would be a theme or plugin that reads a URL parameter with JavaScript and displays it on the page without encoding it first.
Understanding the mechanics is one thing. Understanding what attackers actually do with a successful XSS exploit, that is where the stakes become very concrete.
One of the most immediate consequences of a successful XSS attack is session theft. By injecting a script that reads the browser’s document. cookie value and forwards it to an attacker-controlled server, an attacker can obtain the session token of any user who triggers the payload, including administrators. With that session token, they can impersonate the victim without ever needing their username or password.
Taking this further, attackers can inject malicious admin accounts directly into WordPress or install backdoors through theme and plugin file editors, ensuring continued access even if the initial session expires.
XSS also enables keylogging, injecting JavaScript that intercepts every keystroke a user makes on the affected page and sends it to the attacker. On login pages, this captures usernames and passwords. On checkout pages, it captures payment card numbers.
Once an attacker can execute JavaScript in the context of your site, they can redirect visitors anywhere using window.location.replace() or similar methods. Visitors trying to reach your site end up on phishing pages, malware distribution sites, or fake login portals designed to harvest their credentials.
Attackers also use XSS to inject spam content, display unauthorized advertisements, or deface pages entirely by replacing the DOM content with their own messaging. Any of these outcomes erodes visitor trust and can trigger search engine warnings that devastate organic traffic.
The statistics reinforce how seriously this should be taken. A 2025 mid-year security report found that approximately 41% of WordPress vulnerabilities in the period were rated exploitable in real-world attacks. XSS vulnerabilities in a single plugin can affect hundreds of thousands, or even millions, of sites simultaneously. The LiteSpeed Cache plugin, for instance, had an XSS vulnerability affecting over 4 million active installs.
Most WordPress XSS vulnerabilities originate in one of several predictable locations. Knowing where to look, whether you are a developer auditing your code or a site owner vetting plugins, makes a big difference.
Patchstack research found that 96% of WordPress vulnerabilities are found in plugins. Themes are a secondary but meaningful source. Core WordPress itself is generally well-audited and receives rapid patches.
The reason plugins and themes are so vulnerable is that they are developed independently, often by small teams or solo developers who may not follow security best practices. They handle user input in countless ways, form submissions, AJAX requests, REST API endpoints, shortcode attributes, Gutenberg block attributes, custom widget settings, and any one of these can become an XSS entry point if the input is not properly handled.
WordPress comment forms, user profile fields, and review submissions are classic targets. If a plugin renders comment content without passing it through proper filtering, an attacker can store a payload there that runs for every visitor who loads the post.
Admin notices, those notification bars inside the WordPress dashboard, are a surprisingly common source of reflected XSS vulnerabilities. If a plugin uses a URL parameter to determine what message to display in an admin notice and outputs that value without escaping, an attacker can craft a URL that injects a script into the admin panel. Any administrator who clicks that link has their session exposed.
AJAX handlers and REST API endpoints that accept user input and return it in responses are frequent XSS vectors. Developers sometimes focus on sanitizing form submissions but overlook that AJAX responses and REST API outputs also need proper escaping before they reach the browser.
WordPress shortcodes and Gutenberg blocks often accept attributes that are rendered directly in the page HTML. If those attributes are not sanitized when saved and escaped when rendered, they become viable XSS entry points. Contributor-level users can exploit these by creating draft posts containing malicious payloads, then sending the preview link to administrators to trigger the attack.
For anyone building or customizing WordPress themes and plugins, XSS prevention comes down to three non-negotiable habits: validate input, sanitize on the way in, escape on the way out.
Validation means checking that incoming data matches what you actually expect before you do anything with it. An email field should only accept email-shaped data. An ID field should only accept integers. A URL field should only accept valid URL. Reject or normalize everything else before it goes any further.
Use allowlist approaches where possible, define what is acceptable, rather than trying to block every possible bad value. This is especially important for fields with predictable formats like dropdowns, checkboxes, or numeric ranges.
WordPress provides a purpose-built library of sanitization functions that cover virtually every data type you will encounter:
| Function | Purpose |
sanitize_text_field() | Plain text: names, titles, simple strings |
sanitize_email() | Email addresses |
sanitize_textarea_field() | Multi-line text content |
sanitize_url() / esc_url_raw() | URLs before database storage |
absint() / intval() | Integer ID and numeric values |
wp_kses() | HTML content where only a specific safe subset of tags is permitted |
wp_kses_post() | HTML content using WordPress standard post content allowlist |
A critical mistake to avoid sanitize_text_field() is not an all-purpose security function. It normalizes plain text but does not make values safe to output inside HTML attributes. Sanitizing for storage and escaping for output are separate, equally necessary steps.
Escaping is what prevents stored or reflected data from being interpreted as code when the browser renders it. WordPress provides context-specific escaping functions; using the wrong one for a given context can leave you vulnerable:
| Function | Context |
esc_html() | Content between HTML tags |
esc_attr() | Values inside HTML element attributes |
esc_url() | URLs in href and src attributes |
esc_js() | Data embedded in JavaScript strings |
wp_json_encode() | Data passed as JSON to JavaScript blocks |
Never echo raw $_GET, $_POST, or database values directly into templates, admin notices, or JavaScript without passing them through the appropriate escaping function first.
WordPress nonces are security tokens that verify requests originate from your site and from an authenticated user with the appropriate intent. Add nonces to every form with wp_nonce_field() and verify them with check_admin_referer() on submission. For AJAX actions, use check_ajax_referer().
While nonces do not directly prevent XSS output, they block the chaining of XSS with Cross-Site Request Forgery (CSRF), a common escalation technique where an XSS payload triggers privileged actions like adding admin accounts or installing plugins.
DOM-based XSS often lives entirely in the front-end JavaScript. Replace dangerous DOM manipulation patterns with safe alternatives:
element.innerHTML = userValuewp_localize_script() or inline JSON with wp_json_encode(), never raw echo into script blockseval() or Function() with any user-supplied dataYou do not need to write code to dramatically reduce your site XSS exposure. The most impactful protections available to non-developers are also the most frequently neglected.
Outdated plugins are the primary attack vector for XSS in WordPress. When a vulnerability is disclosed, security researchers publish details, and attackers immediately begin scanning for unpatched sites. Keeping WordPress core, all active themes, and all plugins updated to their latest versions eliminates the vast majority of known XSS vulnerabilities.
Critically, do not just deactivate unused plugins; delete them entirely. Even inactive plugin code can contain exploitable vulnerabilities.
A WAF sits between incoming traffic and your WordPress installation, inspecting requests for known malicious patterns and blocking them before they ever reach your code. For stored and reflected XSS, a good WAF can stop many attacks even when the underlying code has a vulnerability. Reputable security plugins with integrated WAF capabilities are widely available for WordPress.
That said, a WAF is a layer of defense, not a replacement for secure code or timely updates. Treat it as a safety net, not the primary barrier.
A few targeted configuration changes reduce the attack surface significantly:
'DISALLOW_FILE_EDIT', true); to your wp-config.php file. This prevents attackers who gain admin access through XSS from injecting backdoors directly into theme and plugin files via the built-in editor.HTTPOnly) and ensure cookies are only transmitted over HTTPS (Secure), limiting what an attacker can steal through XSS.XSS.A Content Security Policy is an HTTP response header that instructs the browser about which sources of scripts it should trust. A well-configured CSP can prevent the browser from executing injected scripts even when an XSS vulnerability exists in your code, because the injected script comes from an untrusted source.
Start in Report-Only mode (Content-Security-Policy-Report-Only) to observe what a strict policy would block without actually breaking anything, then gradually tighten and enforce.
What to Do If Your Site Has Already Been Compromised
If you suspect an XSS attack has already affected your site, move quickly but methodically.
Treating a compromise as a single incident to fix and forget is a mistake. Use the experience as a trigger to review your full security posture, backup frequency, update hygiene, plugin inventory, and access controls.
The recurring theme in every XSS discussion is that this is not a one-time problem to solve. The WordPress plugin ecosystem sees new vulnerabilities reported constantly. New plugins, new features and new custom code each introduce new potential entry points.
The sites that stay protected are those where security is treated as an ongoing practice: regular updates, periodic security scans, disciplined coding habits, and a culture of vetting new plugins carefully before installation. No single tool or configuration change makes a WordPress site permanently XSS-proof. But the combination of updated software, proper output escaping in custom code, a WAF layer, hardened configuration, and strong backup practices eliminates the overwhelming majority of real-world risk.
XSS is abundant precisely because it is easy to introduce through careless coding, and because it is easy to prevent through disciplined coding. The gap between vulnerable and protected comes down to consistent habits, not exotic technical skill.

Hassan Tahir wrote this article, drawing on his experience to clarify WordPress concepts and enhance developer understanding. Through his work, he aims to help both beginners and professionals refine their skills and tackle WordPress projects with greater confidence.