- Lifetime Solutions
VPS SSD:
Lifetime Hosting:
- VPS Locations
- Managed Services
- Support
- WP Plugins
- Concept

In 2026, the online world will have become more demanding for business owners, digital agencies, and website managers. Everyone now faces two major challenges: improving search engine visibility by making websites fast and optimized, and protecting websites from advanced cyber threats.
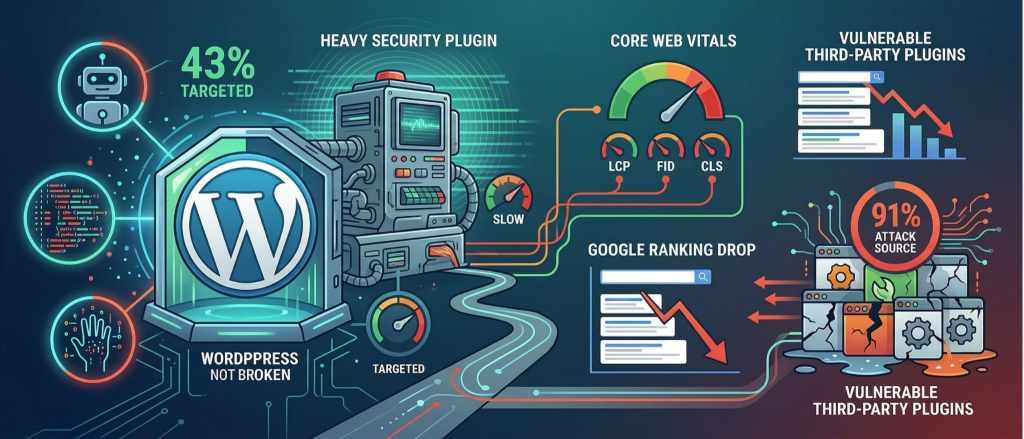
WordPress, which powers around 43% of all websites on the internet, has become the most common target for hackers, automated bots, and cybercriminal groups. At the same time, search engines like Google now strongly penalize websites that provide a slow or poor user experience.
Because of this, website security and SEO are no longer separate tasks. Instead, they work together as a critical requirement for running a successful website today.
Many experts are now reconsidering the traditional approach of using heavy security plugins inside WordPress. These plugins often run many background scans and processes, which can slow down a website. Performance studies show that this extra load can negatively affect Core Web Vitals (CWV), an important factor used by search engines like Google to rank websites. When website speed drops, search rankings can also fall, creating a strange situation where a security plugin meant to protect a website actually harms its visibility and performance.
Recent security reports also reveal an important truth about the WordPress threat landscape. Around 91% of successful WordPress attacks come from vulnerable third-party plugins, not from WordPress itself. In fact, the WordPress core software is rarely the cause of major security breaches, making poorly maintained plugins the biggest security risk for most websites.
To understand the necessity of alternative security frameworks, one must first analyze the mechanical and operational realities of the industry’s most solution Wordfence. Operating as the undeniable heavyweight within the WordPress ecosystem, this plugin protects over 5 million active websites and has historically defined the standard for accessible website defense.
The primary architecture of this incumbent solution is classified as an “endpoint” Web Application Firewall. This means the firewall operates directly within the WordPress application layer, executing via PHP on the host server environment. This deployment model provides distinct, undeniable advantages. Because the firewall runs locally, it has deep awareness of the WordPress environment, including active user sessions, user identity information, and plugin execution states.
The developers of this endpoint solution state that their firewall uses user identity information in over 85% of its firewall rules, allowing a very detailed level of protection that external cloud firewalls often cannot access. In addition, an endpoint firewall preserves end-to-end encryption, meaning it does not require SSL certificates to be terminated at an external proxy, which is often required when using DNS-based cloud security services.
This localized processing mechanism directly impacts database integrity and site speed. Endpoint security solutions often store large logs of blocked traffic, live traffic data, and other security records inside the WordPress MySQL database. Over time, this massive accumulation of data can cause database bloat, which fragments database tables and slows down queries. As a result, websites often require regular database maintenance to maintain acceptable performance.
From a performance perspective, running complex malware scans and firewall rules through local PHP processes can overload server resources and saturate database connections. This can lead to slow response times, especially noticeable through higher Time to First Byte (TTFB) delays.
| Characteristic | Endpoint WAF (e.g., Wordfence) | Cloud-Based WAF (e.g., Sucuri) | Pre-Application WAF (e.g., NinjaFirewall) |
| Execution Location | Local Server (PHP/WordPress) | Network Edge (DNS Routing) | Local Server (Pre-WordPress PHP) |
| Resource Consumption | High (Processes every request locally) | Zero (Traffic filtered before server) | Very Low (Bypasses WordPress core) |
| DDoS Mitigation | Poor (Server collapses under load) | Excellent (Absorbs attacks at the edge) | Poor (Server still receives connections) |
| Contextual Awareness | High (Deep user identity integration) | Low (Operates outside the application) | Moderate (Server-level awareness) |
| Database Bloat | High (Logs stored in local MySQL) | None (Logs stored on provider servers) | Low (Custom logging mechanisms) |
Table 1: Architectural Comparison of Web Application Firewall Deployment Models and Resource Implications.
A profound strategic insight emerging in 2026 is the recognition that application-layer security plugins represent only a single, often superficial layer of defense. Truly strong and resilient security must be integrated at the infrastructure and server level, rather than relying only on WordPress plugins.
Security plugins operating within the WordPress ecosystem are inherently limited by their environment. They are mostly restricted to the PHP application layer, which means they cannot detect threats that exist outside their PHP sandbox. If a sophisticated attacker exploits an operating system vulnerability, uses a compromised SSH key, or gains access through another poorly secured application on the same shared hosting server, a WordPress endpoint security plugin may remain completely unaware of the intrusion.
Additionally, advanced malware can be placed directly into server-level cron jobs or hidden within system memory, allowing it to bypass PHP-based file scanners used by most WordPress security plugins.
As the limitations of traditional perimeter defenses and basic endpoint firewalls become more evident, the industry is seeing faster adoption of Runtime Application Self-Protection (RASP) technologies within complex WordPress environments. RASP represents a major advancement in security, moving beyond simple network traffic blocking to deep application-level analysis that monitors how the application behaves in real time.
RASP operates by embedding sophisticated telemetry sensors directly into the application’s codebase or the runtime environment itself (such as the PHP engine executing the WordPress core). Unlike a traditional Web Application Firewall, which relies heavily on analyzing HTTP request syntax and matching it against static, potentially outdated signature databases, RASP continuously monitors the actual execution flow of the application in real-time. It rigorously evaluates database queries, file system interactions, configuration state changes, and memory allocations as they dynamically occur.
The critical advantage of RASP is contextual awareness. If a highly obfuscated, seemingly benign HTTP request successfully bypasses a traditional WAF, but subsequently attempts to execute an unauthorized system command or alter an unexpected database table within the application logic, the RASP system detects the behavioral anomaly contextually and terminates the specific process immediately. This deterministic, behavior-based approach dramatically minimizes false positives. It provides an unparalleled defense mechanism against previously unknown zero-day exploits, making it an indispensable component for enterprise-grade WordPress security strategies moving forward.
MalCare has engineered a highly sophisticated, data-driven approach to WordPress security, distinctly and purposefully separating itself from traditional endpoint competitors through its proprietary cloud-based architecture. Intensive comparative testing consistently highlights MalCare as the most comprehensive direct alternative, offering advanced protection mechanisms without the associated performance penalties.
The defining characteristic of the MalCare infrastructure is its off-site scanning mechanism. Rather than executing highly intensive file comparisons and malware signature checks on the live Origin server, MalCare utilizes a synchronization protocol to seamlessly copy the website’s files and database to its own proprietary, external servers. The complex malware analysis, utilizing over 100 deep behavioral signals and AI-powered heuristic detection models—occurs entirely on this external infrastructure.
This architectural decision ensures that rigorous, deep-level security scans can run continuously and frequently without inflicting any performance penalty, CPU drain, or memory exhaustion on the Origin server. This is a massive strategic advantage for preserving Time to First Byte (TTFB) and maintaining pristine Core Web Vitals metrics.
Furthermore, MalCare fundamentally disrupts the industry standard regarding malware remediation by providing instant, automated, one-click malware removal. While many premium competitors require users to submit a support ticket and wait hours or even days for human security analysts to manually clean an infected site, MalCare algorithmically isolates and purges malicious code injections in a matter of minutes. This rapid recovery capability drastically reduces the window of vulnerability and mitigates the risk of search engine blocklisting.
Sucuri maintains its position as a dominant heavyweight in the global cybersecurity sector, positioned primarily as an enterprise-grade, edge-level defense system. Rather than attempting to secure the application locally, Sucuri’s core operational strength lies in its cloud-based Web Application Firewall (WAF), which intercepts, sanitizes, and filters traffic via global DNS routing.
By requiring a DNS change, Sucuri routes all incoming website traffic through its proprietary global network before it ever reaches the user’s Origin server. This network-edge interception fundamentally shields the server from malicious load, easily absorbing massive Distributed Denial of Service (DDoS) attacks and deflecting automated brute-force attempts before they consume local bandwidth.
This edge-level security is coupled with a highly effective global Content Delivery Network (CDN) that aggressively caches static assets. This offloading of traffic not only secures the site but also accelerates content delivery globally, providing tangible SEO benefits through improved global load times and latency reduction.
However, a rigorous analysis of Sucuri’s architecture reveals notable drawbacks, particularly regarding malware detection and remediation workflows. While the DNS firewall is exceptional at prevention, its remote malware scanner has documented limitations. Because it primarily scans the front-end rendering of the site externally, it frequently misses highly sophisticated, deeply embedded PHP malware or database-level injections that do not immediately appear on the user-facing interface.
When a security compromise does occur, Sucuri relies entirely on professional human labor to perform the cleanup. While this ensures expert remediation, it introduces a significant time delay during which the site remains vulnerable and may face search engine penalties. Furthermore, its premium pricing structure, often starting at $199 per year, positions it more as a costly, comprehensive security solution rather than an accessible option for smaller websites or independent bloggers.
Patchstack approaches the WordPress security landscape from a fundamentally different vector, intentionally abandoning traditional firewall and malware scanning paradigms in favor of highly targeted vulnerability management and automated virtual patching. The statistical reality drives this strategic focus that 91% of WordPress exploits target vulnerabilities found in third-party plugins.
Patchstack operates a massive, centralized vulnerability intelligence network, fueled by an active community of security researchers participating in gamified bug bounty programs. While the incumbent solution utilizes high-dollar payouts (up to $14,400) to attract critical zero-day discoveries, Patchstack leverages a 10-level XP-based gamification system and monthly competitions to crowd-source vulnerability data across a wide range of plugins, including those with lower installation counts.
When a new vulnerability is discovered within a specific plugin or theme, Patchstack instantly deploys a highly specific, on-demand security rule directly to the user’s website. This “virtual patch” seamlessly neutralizes the exploit vector before the plugin developer releases an official update, and crucially, without requiring the site administrator to manually log in and initiate an update sequence.
Because Patchstack only triggers rules on demand when a known vulnerability is present on the site, its processing footprint is exceptionally minimal. It causes zero noticeable impact on server performance, making it an ideal, frictionless layer in a multi-tooled security stack. However, it is imperative to understand that Patchstack is explicitly not a holistic security suite; it entirely lacks comprehensive malware scanning, broad-spectrum bot defense, and general firewall capabilities. It is a surgical, developer-focused tool favored by agencies managing vast client portfolios who require automated mitigation of the specific supply-chain vulnerabilities that cause the vast majority of modern breaches.
| Security Solution | Core Architectural Focus | Starting Annual Price | Primary Advantage | Primary Limitation |
| MalCare | Cloud Scanner / One-Click Removal | $99/year | Zero server impact & instant cleanup | The free version is limited to scanning |
| Sucuri | DNS Edge WAF / CDN | $199/year | Exceptional DDoS mitigation | Slow manual cleanup / High cost |
| Patchstack | Virtual Patching / Vulnerability Intel | $60/year ($5/mo) | Surgical protection for 3rd party plugins | Lacks general WAF and malware scans |
| Solid Security | Application Hardening / Access Control | $99/year | Excellent 2FA and login security | Lacks automated malware removal |
| NinjaFirewall | Pre-Application Endpoint WAF | Free / Premium available | Highly lightweight PHP filtering | Complex configuration for beginners |
Formerly operating under the highly recognized brand iThemes Security before a comprehensive rebranding in 2023, Solid Security focuses strictly on hardening the core WordPress application and controlling access points. It is engineered to specifically mitigate the most common and statistically prevalent attack vectors—such as automated brute-force login attempts and the exploitation of compromised credentials, which account for a large percentage of successful unauthorized intrusions.
Solid Security excels in enforcing robust password policies, implementing Two-Factor Authentication (2FA) across all user roles, dynamically renaming default database prefixes, aggressively locking out repeated failed login attempts, and tracking detailed user activity logs to monitor internal threat vectors. It provides a visually intuitive interface that evaluates the site’s overall security posture, making security hardening accessible and actionable for non-technical administrators.
Despite its undeniable utility in access control, Solid Security possesses significant limitations when used as a standalone defense mechanism against advanced threats. It fundamentally lacks a sophisticated Web Application Firewall (WAF) capable of stopping advanced code injections, and it does not provide automated malware scanning or remediation services.
Consequently, while it remains a cost-effective solution for basic hardening and login protection, it fails to deliver the comprehensive, full-spectrum security required to defend against advanced zero-day exploits or complex server-level attacks.
NinjaFirewall represents a unique and highly technical architectural middle ground in the security landscape. It is technically an endpoint firewall that resides locally on the server, yet it is engineered to intercept and evaluate traffic before the WordPress environment is fully loaded.
By utilizing PHP powerful auto_prepend_file configuration directive, NinjaFirewall evaluates incoming HTTP requests at the very beginning of the PHP execution cycle, aggressively blocking SQL injections, Cross-Site Scripting (XSS), and malicious payloads with minimal processing overhead. Because it stops threats before the WordPress core, the database, and the plugin ecosystem are initialized, it prevents malicious traffic from consuming the majority of server resources.
This pre-application filtering capability makes NinjaFirewall significantly faster and less resource-intensive than traditional endpoint WAFs. It provides deep logging capabilities, advanced filtering rules, and true pre-execution defense, making it a highly respected and frequently recommended tool among system administrators who prioritize server efficiency.
When intelligently layered with a specialized external malware scanner, NinjaFirewall enables a highly optimized, dual-layer security setup that meets both enterprise-level security requirements and SEO performance benchmarks.
For operators constrained by budget, the market offers robust free alternatives that provide substantial protection without the aggressive monetization strategies of the incumbent solution.
All In One WP Security & Firewall (AIOS): Recognized as a premier free option, AIOS provides a comprehensive suite of security features wrapped in an intuitive, visual dashboard. It utilizes a proprietary Security Strength Meter that visually tracks overall protection based on activated features, guiding users from basic to advanced hardening.28 Its firewall relies heavily on efficient .htaccess rules to block malicious queries, XSS attacks, and bad bot traffic before they invoke PHP. It effectively manages login lockdowns, IP blacklisting, and database prefix modifications. However, its critical limitation is the complete lack of a malware scanner or cleanup service, making it an excellent preventative tool but useless for post-breach remediation.
Jetpack Security: Developed by Automattic, the corporate entity behind WordPress.com, Jetpack offers a vast suite of services, including downtime monitoring, brute-force protection, and secure authentication in its free tier. Its premium tiers introduce robust, real-time automated backups and automated malware scanning. While highly reliable, Jetpack’s modular nature often introduces unnecessary bloat if administrators only require specific security features rather than its full suite of marketing and performance tools.
CleanTalk and BulletProof Security: CleanTalk operates as a highly efficient, low-noise cloud firewall and anti-spam solution, leveraging global databases to block malicious IPs dynamically. BulletProof Security targets highly technical administrators, utilizing complex .htaccess server rules and quarantine protocols to lock down root files, providing immense power but requiring a steep learning curve.
The conceptual separation of website security operations from Search Engine Optimization (SEO) strategies is a deprecated and fundamentally flawed model. In the modern algorithmic environment of 2026, an organization’s security posture is a direct, measurable ranking factor, significantly influencing both search engine crawler behavior and user experience metrics.
Search engines demand lightning-fast, mobile-first, and highly stable user experiences. The strict enforcement of Core Web Vitals as primary ranking signals means that technical performance is directly tied to organic visibility. Effective WordPress optimization requires the stabilization of three critical metrics: Largest Contentful Paint (LCP), Interaction to Next Paint (INP), and Cumulative Layout Shift (CLS).
Security plugins fundamentally and directly alter how a WordPress environment processes external requests, queries its database, and renders content to the browser. The average modern WordPress site uses 25+ plugins, and adding poorly optimized, resource-heavy security scripts can increase Time to First Byte (TTFB) by 300 to 800 milliseconds per component. TTFB measures the exact time between a browser request and the first byte of data returned by the server.
When a heavy endpoint security plugin executes continuous file integrity monitoring, live traffic logging, or database scanning on the local server, it monopolizes critical PHP workers and server CPU cycles. This resource monopolization prevents the server from swiftly compiling and delivering HTML payloads to search engine crawlers and end-users, which directly and unavoidably tanks LCP scores.
A delay of merely one second in page load time has been empirically shown to drastically reduce conversion rates, with 53% of mobile users abandoning sessions entirely if the site exceeds a strict three-second render threshold. Therefore, selecting a highly optimized security infrastructure that deliberately offloads processing power, such as deploying cloud-based scanners like MalCare or edge-level firewalls like Sucuri, is not merely a defensive security decision; it is a fundamental, non-negotiable SEO necessity.
A secondary, often overlooked SEO benefit of advanced security implementation is the preservation of search engine crawl budgets. Malicious bots, scrapers, and automated vulnerability scanners constantly target unprotected WordPress sites, consuming server bandwidth and PHP execution time. If a server is overwhelmed serving 404 pages to malicious bots attempting to find vulnerabilities, it will respond slowly when Googlebot tries to crawl and index new content.
By deploying a highly efficient WAF at the network edge or via pre-application filtering, administrators can completely block unnecessary bot traffic. This deliberate traffic shaping saves massive server resources, allowing the Origin server to respond instantly to legitimate search engine crawlers, thereby increasing crawl frequency, accelerating the indexing of new content, and improving overall SERP visibility.
Beyond the nuances of pure speed metrics, the successful injection of malicious code represents a catastrophic, potentially unrecoverable event for historical SEO equity. When a WordPress site is compromised via a plugin vulnerability or brute-forced credentials, attackers rarely destroy the site; instead, they silently exploit its search engine authority.
They frequently deploy complex SEO spam, injecting hidden pharmaceutical, counterfeit, or gambling links deep into the database, generating thousands of malicious indexed pages. Alternatively, they may implement conditional redirects that hijack legitimate organic traffic, sending mobile users from search engines directly to external phishing domains or malware distribution networks.
Once search engine algorithms or automated safety crawlers detect these anomalies, the domain is rapidly placed on global blocklists. The resulting “This site may be hacked” SERP warning or browser-level “Deceptive site ahead” warnings instantly destroy click-through rates (CTR) and severely damage user trust.
Recovering from a search engine penalty caused by a security breach requires forensic malware cleanup, submitting reconsideration requests, and enduring months of reduced organic traffic while trust is rebuilt. Consequently, proactive, cloud-based security is the ultimate safeguard for protecting long-term SEO investments.
| SEO Metric | Impact of Heavy Endpoint Plugins | Impact of Cloud/Edge Security |
| Time to First Byte (TTFB) | High Degradation (Server overload) | Protected/Improved |
| Largest Contentful Paint (LCP) | Delayed (Due to slow HTML delivery) | Accelerated (via CDN caching) |
| Crawl Budget Efficiency | Poor (Server wastes resources on bots) | Excellent (Bots blocked at the edge) |
| Database Response Time | Slowed (Due to massive security logs) | Unaffected (Logs stored externally) |
Securing the platform from external threats is the operational prerequisite; optimizing it for maximum algorithmic visibility is the ultimate commercial objective. In 2026, the deployment of specialized, highly configured SEO plugins remains fundamental to managing technical site architecture, content syntax, and the flawless execution of structured data.
The modern SEO plugin serves as the central nervous system for achieving technical search compliance. These tools do not natively increase rankings by their mere installation; rather, they provide the necessary, user-friendly interfaces to structure content so that complex search engine algorithms can ingest, parse, and index it flawlessly.
The primary contenders dominating this space, Rank Math, Yoast SEO, and All in One SEO (AIOSEO), offer overlapping core functionalities that are considered non-negotiable for digital visibility in highly competitive niches.
A definitive, powerful differentiator in 2026 enterprise SEO strategy is the aggressive, flawless implementation of advanced Schema Markup (Structured Data). Search engines increasingly bypass standard organic results, relying heavily on structured data to populate Rich Snippets, Knowledge Panels, and AI-driven search experiences directly at the top of the SERP.
Advanced SEO plugins like Rank Math seamlessly integrate sophisticated Schema generators that dynamically inject perfectly formatted JSON-LD markup directly into the HTML DOM. By explicitly defining data entities, such as identifying a page as an “Article”, a “Product” with aggregate star reviews and pricing data, or a “Local Business” with exact geospatial coordinates, administrators eliminate algorithmic ambiguity.
This precise categorization allows search engines to understand the exact context and value of the content, dramatically increasing the probability of capturing high-visibility SERP features that drive exponential organic traffic.
Furthermore, ensuring seamless technical interoperability between SEO plugins and security configurations is absolutely vital. Aggressive firewall rules, particularly those configured manually by inexperienced administrators, must be carefully audited to ensure they do not block legitimate search engine user-agents (such as Googlebot or Bingbot) from crawling the site, or incorrectly cache critical, dynamic XML sitemaps, which would immediately halt all indexing efforts.
The ultimate objective of a digital platform is not merely to exist securely, but to perform efficiently and rank prominently within global search engines. Achieving this synthesis requires a calculated, multi-layered architectural approach that rejects monolithic, resource-heavy solutions in favor of specialized, interoperable components. The most security-conscious agencies in 2026 are actively running 3 to 5 different, lightweight solutions in overlapping layers.
By moving heavy security tasks to cloud security services and global edge networks, website administrators can keep their origin server focused on what matters most: delivering fast, optimized, and reliable content to visitors and search engine crawlers. Instead of overloading the server with complex security processes, these tasks are handled externally, which helps maintain better speed and stability.
This smart combination of lightweight security infrastructure and strong technical SEO practices helps websites stay protected from modern cyber threats while also improving search visibility, user experience, and engagement. In the highly competitive online environment of 2026, this balanced approach helps businesses attract more visitors, rank higher in search results, and increase revenue.

Hassan Tahir wrote this article, drawing on his experience to clarify WordPress concepts and enhance developer understanding. Through his work, he aims to help both beginners and professionals refine their skills and tackle WordPress projects with greater confidence.